AV-Comparatives Recognizes Bitdefender as Strategic Leader in Endpoint Protection and Response

- Bitdefender named Strategic Leader in latest EPR report, the highest certification level
- The report measures efficacy and includes comprehensive methods for measuring ROI and TCO
- Bitdefender correlation capabilities and timelines for threat propagation features were highlighted
We are excited to announce that Bitdefender has been confirmed as a Strategic Leader in the latest “Endpoint Prevention and Response (EPR)” report from AV-Comparatives. The test assessed and compared the performance of 10 endpoint cybersecurity solutions, including Bitdefender GravityZone Business Security Enterprise. AV-Comparatives is an independent, certified testing lab that is audited every year to ensure that tests are unbiased and independent. We highly value their open methodology, and efforts to cut through the marketing and test solutions in a near real-world setup. The ultimate competitor of all participants are threat actors, and independent evaluations help security vendors learn from these exercises and improve our security technology.
Effectiveness
Some industry tests are focused on prevention capabilities (for example, the Business Security Test from AV-Comparatives), while others are focused on detection capabilities (for example, MITRE ATT&CK Evaluations). The EPR report is an ambitious, comprehensive evaluation that reflects the everyday reality of enterprise use cases, combining both prevention and detection capabilities into a single report.
A total of 50 scenarios were executed against deployed security solutions, evaluating them from the context of the entire attack kill chain. Vendors don’t know in advance when exactly the test will be performed, nor any other details about the attacks. In real life, threat actors also don’t tell victims when and how they are going to be attacked.
The EPR report differentiates between active response (action is prevented) and passive response (action is detected and reported but requires human interaction). An attack progresses through three different phases, and prevention and detection are measured for each separately:
- Phase 1 (Compromise and Foothold) – Initial Access, Execution, Persistence
- Phase 2 (Internal Propagation) – Privilege Escalation, Defense Evasion, Credential Access, Discovery, Lateral Movement
- Phase 3 (Asset Breach) - Collection, Command and Control, Exfiltration, Impact
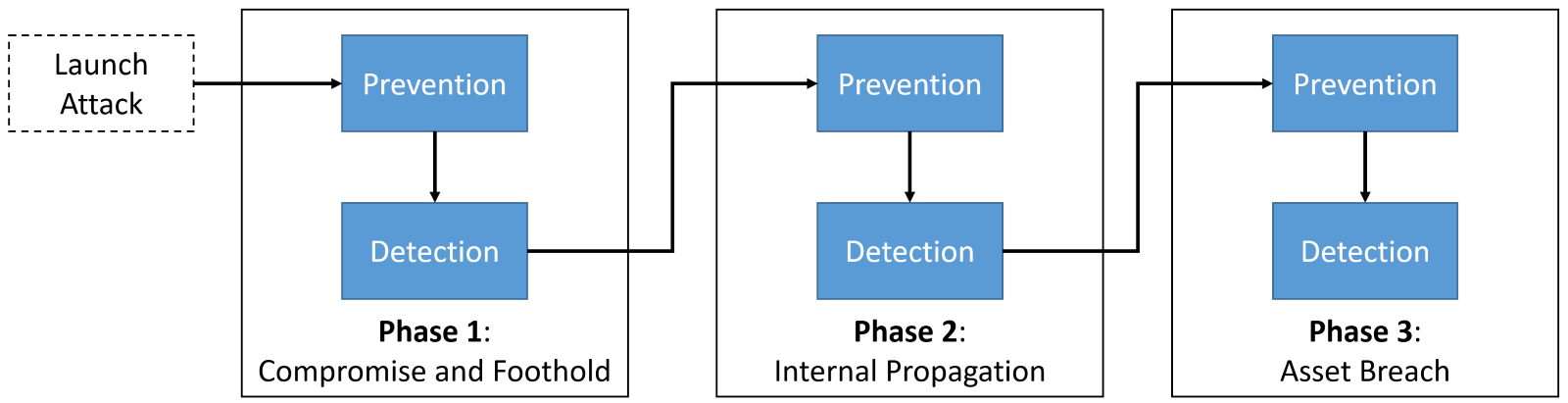
Figure 1: Successful prevention stops the attack flow, as a threat has been eliminated. Successful detection reduces the penalty but doesn’t stop the attack from progressing to the next phase.
The goal is to block the attack before it can reach phase 3, the final phase where threat actors start carrying out their ultimate objective. If prevention and detection fail in this final phase, threat actors have achieved a security breach without being detected. This year, half of the participating vendors failed to prevent the security breach and decided to stay anonymous in the EPR report.
You can find the full report on the performance of Bitdefender here. The Bitdefender solution achieved a cumulative Active Response rate of 100%, preventing security breaches in all tested scenarios. This is an incredible accomplishment and recognition of Bitdefender’s position in the endpoint security, endpoint detection and response, and endpoint protection and prevention market.
Measuring false positives, ROI, and TCO
Combining prevention and detection into a single evaluation report is one of the unique features of this report. The challenge with this approach is vendors may configure solutions for aggressive protection, artificially improving prevention ratings, but also generating a lot of noise and false alarms.
Accuracy, actionability, and detection of false positives are important criteria for any endpoint security evaluation. A high number of false alerts impacts different parts of the organization, from end users (security should not limit productivity) to business (with an increase of TCO/ROI), to the security team itself (an overworked team).
The EPR report deals with this challenge by including data about Operational Accuracy and Workflow Delay costs. Operational Accuracy simulates typical user activity (opening files, browsing), while monitoring if the endpoint security solution impacts productivity (false positives). Workflow Delay adds a penalty for using the sandbox solution. Bitdefender had a low impact for workflow delay and was the only vendor with no cost penalization for operational accuracy. In all tested scenarios, Bitdefender achieved zero false positives. We are proud of our high rate of prevention and detection rating. However, it’s the combination of that – with no false positives – that is most important for our customers.
Information from effectiveness testing is combined with product cost and accuracy data to calculate the total cost of ownership. The Bitdefender solution achieved a Strategic Leader certification by having a very high return on investment and a very low total cost of ownership. More information about the TCO methodology and data is available in the full report.
Actionability
Having effective security operations is one of the most important factors in stopping security incidents from becoming security breaches. The EPR report includes quantifiable data such as false positives, but there are more subjective elements which improve the effectiveness and actionability of security teams.
AV-Comparatives said the following about the Bitdefender platform in the EPR report: “It should be noted that the product has very good correlation capabilities and timelines for threat propagation. For example, when some attacks were detected in a later phase, the product traced them back to their origin and provided very detailed information.”
Our solution for detection and response (Bitdefender GravityZone XDR) was designed as a Native XDR solution (read more about Native XDR vs Open XDR). It’s a solution that has out-of-the-box integration with additional telemetry sources, making it easy to deploy with a shorter time to value. One of the promises of native XDR is better accuracy, a promise validated by zero false positives in our results.
Our Native XDR platform is only part of our efforts to build a more actionable and approachable detection and response platform. One of the most important features is our Incident Advisor – an overview that summarizes the most critical information about an incident on a single page. Incident Advisor correlates data from multiple sources, presenting them in a format that minimizes the time required for investigation and response. This includes information about what happened, who was impacted, how the incident occurred, and recommended actions. Extended root cause analysis is available for further investigation, including visualizing the kill chain to allow security analyst to interrupt it before it fully develops.
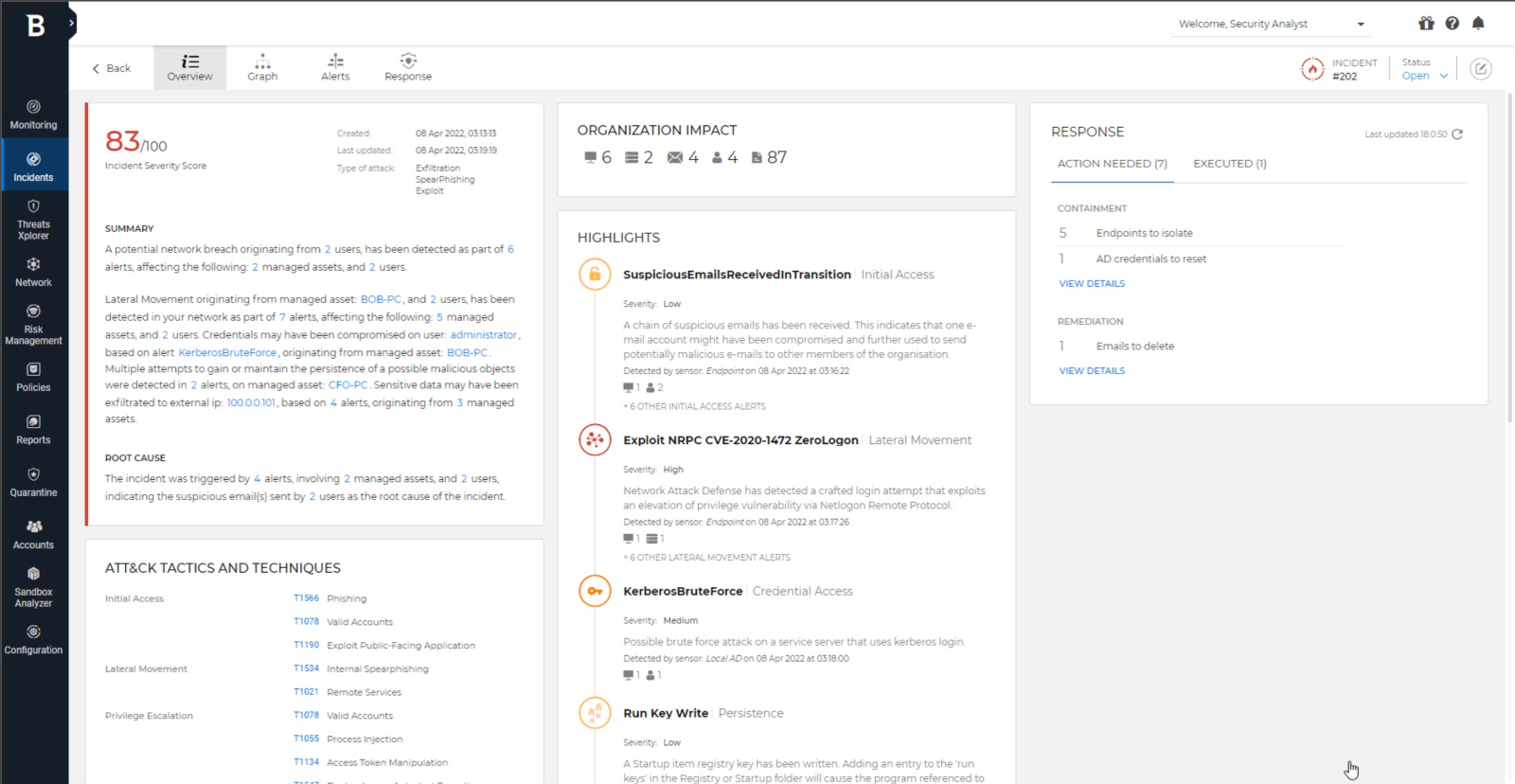
Figure 2: Incident Advisor correlates hundreds of events and provides all key information on a single page
Throughout the investigation, we offer recommendations and guided and automated response actions. Depending on deployed sensors, different categories of actions are available, making it easy to identify actions that can be used by even a junior analyst. Watch our demo to see this solution in action or try it in your own environment.
Customers can also enhance their security operations with optional Bitdefender managed detection and response service (Bitdefender MDR). For customers that don’t have security operations center (SOC) or need to enhance their security staff, you can rely 24/7 on our elite team of cybersecurity experts and a fully staffed SOC for proactive protection.
Conclusion
The best protection against modern attacks is to implement a defense-in-depth architecture. Start with reducing your attack surface and then leverage automated prevention controls to eliminate, as early as possible, most security incidents. For the few incidents that may get through your defenses, rely on detection and response capabilities, adopted as a service or as a product.
Implementing multiple layers of security should not be a checkbox exercise – the quality of each layer must be thoroughly and regularly evaluated. While a high malware protection rate and a low number of false alerts are good indicators of an accurate security solution, consider also other decision factors – for example, if a solution is Native XDR or Open XDR, and how easy it is to implement, configure, and maintain the product.
Third-party, independent testing with a well-defined methodology offers invaluable insights into the capabilities of leading cybersecurity companies so you can make informed decisions. Cybersecurity is a game of cat and mouse, with both sides continuously innovating and improving tools and techniques, and security vendors need to prove their solutions are effective, accurate, and provide consistent results.
Learn more about Endpoint Prevention and Response with the full report from AV-Comparatives.
tags
Author
Bitdefender is a cybersecurity leader delivering best-in-class threat prevention, detection, and response solutions worldwide. Guardian over millions of consumer, enterprise, and government environments, Bitdefender is one of the industry’s most trusted experts for eliminating threats, protecting privacy, digital identity and data, and enabling cyber resilience. With deep investments in research and development, Bitdefender Labs discovers hundreds of new threats each minute and validates billions of threat queries daily. The company has pioneered breakthrough innovations in antimalware, IoT security, behavioral analytics, and artificial intelligence and its technology is licensed by more than 180 of the world’s most recognized technology brands. Founded in 2001, Bitdefender has customers in 170+ countries with offices around the world.
View all postsRight now Top posts
FOLLOW US ON SOCIAL MEDIA
SUBSCRIBE TO OUR NEWSLETTER
Don’t miss out on exclusive content and exciting announcements!
You might also like
Bookmarks








