Pinch yourself because it’s sometime hard to believe in 2017 – but one of the biggest threats your company faces are old-fashioned and simplistic phishing attacks.
A phishing attack, arriving via email, might successfully trick one of your users into unwittingly hand over their password details to a criminal – with a potentially huge impact to your business.
Imagine, for instance, that you are one of the many companies which has chosen to make Microsoft Office 365 a key technology – providing email and collaboration services to your workers.
And then one of your staff receives an email like this:

If your user has received proper security awareness training they might treat the email with suspicion. They might even be smart enough to contact your company’s IT support team and ask them to confirm if the message is legitimate, and what they should do about it.
But all too many users would probably simply click on the link, and find themselves taken to a phishing webpage designed to steal their credentials.

So far, so ordinary. After all, we’ve all read about the danger of phishing attacks many times before.
But things get different when it’s your corporate email system that is being accessed by an unauthorised party.
Once inside your email system, a hacker can access not only your inbox but also your distribution lists. And they can now convincingly pose as a member of your organisation.
For instance, if you were in the business of supplying goods and services to other companies, the hacker can now access your distribution lists and target other companies with convincing emails and realistic-looking invoices.
Messages your customers receive from a hacker who has already compromised your email system are going to look much more convincing, and could result in your clients transferring large sums of money into a scammer's bank account and you losing customer trust and future business.
Remember – this isn’t the case of a hacker forging your email headers to pretend that the messages they are sending are coming from your business’s servers. They really are originating from insider your company’s email system. A compromised business email system.
If you don’t act now to harden your defences and make it difficult for an attacker to breach your Office 365 system via this technique, then you have a ticking time bomb on your hands.
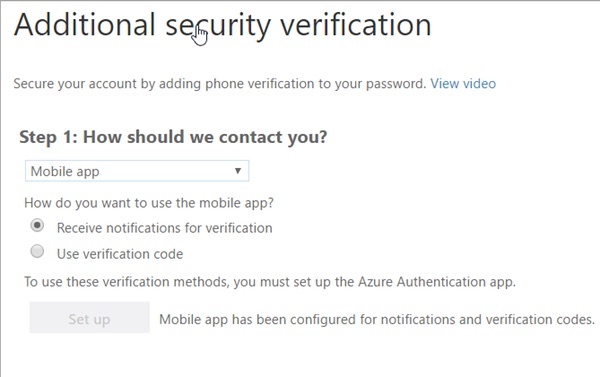
Fortunately, Microsoft has made it easy for Office 365 administrators to set up multi-factor authentication for their users, which adds an additional layer of security.
Even if a user has been tricked into handing over their password (perhaps by a phishing email) or has made the mistake of reusing credentials or chosen a weak, easy-to-crack password, an unauthorised third-party will find it much hard – if not impossible - to gain access to the account.
Remember. Most of the time the trick to avoiding being hacked is not to make yourself 100% secure, but just to make yourself more difficult and time-consuming to hack than another organisation.
Often it is the case that a less attractive target, making yourself a harder nut to crack, is enough to avoid the unwanted attention of hackers.
But don’t rest on your laurels and think that implementing multi-factor authentication is the end of the road when it comes to securing your business’s Office 365 installation.
There are additional protections you can put in place, such as enforcing strong passwords, managing privacy settings, and forcing the use of Outlook Web Access for users connecting from unmanaged devices (making it harder to download entire email databases). Many of these are described on Microsoft’s Office 365 security webpages.
But perhaps most importantly of all, the key thing is to recognise that most security breaches occur because of human failing.
A sensible defence-in-depth solution always recognises the importance of raising awareness inside your company about security issues, and training staff in best practices on how to avoid putting the business’s data and finances at risk.






